I will start in Fall 2024 as an Assistant Professor in the Department of Computer Science at Virginia Tech, and also as a member of the Virginia Tech Center for Quantum Information Science and Engineering. Please contact me at skhatri [at] vt.edu if you find the following research topics interesting, and you would like to pursue a Master’s, PhD, or postdoc with me!
Please see here for the official postdoc job advertisement and to submit your application.
At a glance
(Click here for a PDF)
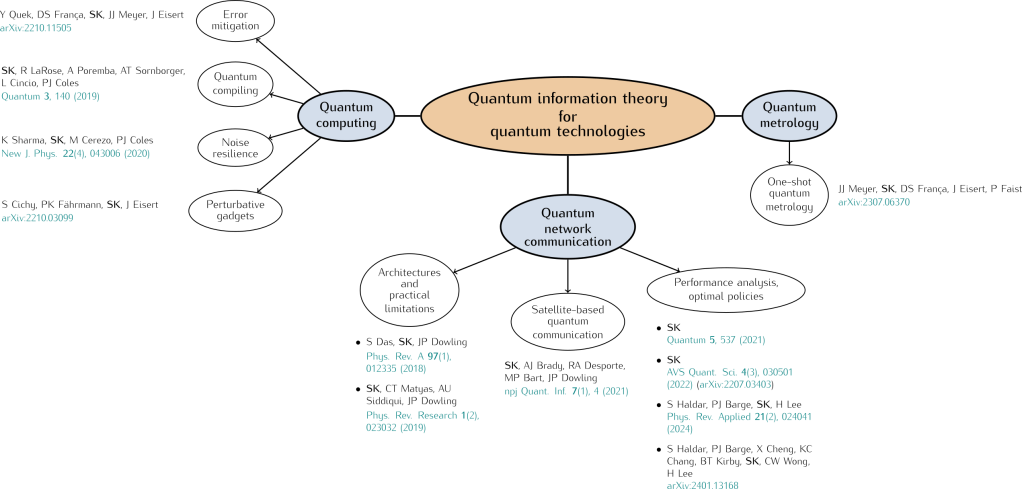
Broadly speaking, my goal and vision is to use the framework of quantum information theory to develop theoretical tools that will allow us to rigorously understand the performance and limitations of quantum technologies — such as quantum computing, communication, and sensing — now and into the future.
Quantum computing
We have now reached a point where small-scale quantum computers (approaching 100 qubits) are now becoming available. These quantum computers are not fault-tolerant, and the qubits are noisy. An interesting area of research is focused on what we can do with such Noisy Intermediate-Scale Quantum (NISQ) devices. An interesting class of quantum algorithms that has gained plenty of attention recently is the class of variational hybrid quantum-classical algorithms, a prominent example of which is the Variational Quantum Eigensolver (VQE). I have recently worked on the possibility of mitigating barren plateaus for variational quantum algorithms using perturbative gadgets, the fundamental limitations of quantum error mitigation, and the impact of non-unital noise on barren plateaus and noisy random quantum circuits more generally.
Here is a talk I gave in 2022 on hybrid quantum-classical algorithms at a summer school.
- Noise-induced shallow circuits and absence of barren plateaus [arXiv]
Antonio Anna Mele, Armando Angrisani, Soumik Ghosh, SK, Jens Eisert, Daniel Stilck França, Yihui Quek - Exponentially tighter bounds on limitations of quantum error mitigation [arXiv]
Yihui Quek, Daniel S. França, SK, Johannes J. Meyer, Jens Eisert - Non-recursive perturbative gadgets without subspace restrictions and applications to variational quantum algorithms [arXiv]
Simon Cichy, Paul K. Faehrmann, SK, Jens Eisert - Noise Resilience of Variational Quantum Compiling [arXiv] [New Journal of Physics] [slides]
Kunal Sharma, SK, Marco Cerezo, Patrick J. Coles - Quantum-assisted quantum compiling [arXiv] [Quantum] [slides]
SK, Ryan LaRose, Alexander Poremba, Lukasz Cincio, Andrew T. Sornborger, Patrick J. Coles
Other relevant work: arXiv:1801.00862, arXiv:1304.3061, arXiv:1411.4028
Quantum networks
Although small-scale quantum computers are now available, they are currently not at the point where they can be useful for meaningful computations tasks (that current classical computers can’t already do). On the other hand, the technology for quantum communication tasks (such as QKD; see below) is mature enough now that quantum communication can be performed over relatively long distances between a handful of nodes.
The next step in quantum communication is to extend small-scale, point-to-point communication to communication between multiple parties in a quantum network, with the grand vision being the realization of a Quantum Internet, an interconnected network of quantum networks much like the internet we currently have. In addition to quantum communication applications (such as quantum key distribution), a quantum internet could allow us to scale-up quantum computers, by linking the small-scale quantum computers that we currently have and performing large-scale quantum computations in a distributed fashion.
Building large-scale quantum networks remains a challenging experimental task. My work in this area has been centered around the questions: how do we assess the performance of a quantum network? How good should our devices be in order to attain certain performance requirements? In order to answer these questions, my colleagues and I have been working on developing a general model of a quantum network and using this model, along with reinforcement learning algorithms, to develop quantum communication protocols such as multipartite entanglement distillation protocols and quantum routing protocols.
- Multipartite entanglement distribution in Bell-pair networks without Steiner trees and with reduced gate cost [arXiv]
S. Siddardha Chelluri, SK, Peter van Loock - Reducing classical communication costs in multiplexed quantum repeaters using hardware-aware quasi-local policies [arXiv]
Stav Haldar, Pratik J. Barge, Xiang Cheng, Kai-Chi Chang, Brian T. Kirby, SK, Chee Wei Wong, Hwang Lee - Fast and reliable entanglement distribution with quantum repeaters: Principles for improving protocols using reinforcement learning [arXiv] [Phys. Rev. Applied]
Stav Haldar, Pratik J. Barge, SK, Hwang Lee - On the design and analysis of near-term quantum network protocols using Markov decision processes [arXiv] [AVS Quantum Science]
- Policies for elementary links in a quantum network [arXiv] [Quantum] [slides] [talk]
- Spooky action at a global distance: analysis of space-based entanglement distribution for the quantum internet [arXiv] [npj Quantum Information] [slides]
SK, Anthony J. Brady, Renée A. Desporte, Manon P. Bart, Jonathan P. Dowling
News article about the paper: Why the quantum internet should be built in space - Practical figures of merit and thresholds for entanglement distribution in quantum networks [arXiv] [Physical Review Research] [slides]
SK, Corey Matyas, Aliza Siddiqui, Jonathan P. Dowling - Robust quantum network architectures and topologies for entanglement distribution [arXiv] [Physical Review A]
Siddhartha Das, SK, Jonathan P. Dowling
General papers: arXiv:0806.4195, Quantum internet: A vision for the road ahead, Why the quantum internet should be built in space
See this How Stuff Works article, in which I talk about the future quantum internet.
Measures of non-Markovianity of open quantum systems
- Fundamental limits on quantum dynamics based on entropy change [arXiv] [Journal of Mathematical Physics]
Siddhartha Das, SK, George Siopsis, Mark M. Wilde
Contributed talk at CQIQC-VII, Toronto.
Quantum Shannon Theory/Fundamental Limitations of Quantum Communications
Work in quantum Shannon theory is centered around finding the fundamental limits of quantum information processing tasks. One such task is communication, and the goal is to determine the maximum rate of communication possible over a given quantum channel, a quantity referred to as the communication capacity of the quantum channel. There are several different types of communication over a quantum channel, such as classical communication, private communication, and quantum communication. My work in this area has looked at various upper and lower bounds on these communication types.
- Information-theoretic aspects of the generalized amplitude damping channel [arXiv] [Physical Review A]
SK, Kunal Sharma, Mark M. Wilde - Second-order coding rates for key distillation in quantum key distribution [arXiv]
Mark M. Wilde, SK, Eneet Kaur, Saikat Guha - Bounding the forward classical capacity of bipartite quantum channels [arXiv]
Dawei Ding, SK, Yihui Quek, Peter W. Shor, Xin Wang, Mark M. Wilde
Symmetric extendibility of quantum states
For a given bipartite quantum state ρAB (describing, say, the quantum systems held by Alice and Bob), does there exist another quantum system B′ such that the joint tripartite state ρABB′ satisfies TrB′[ρABB′] = TrB[ρABB′] = ρAB? If such a tripartite state exists, we call ρAB symmetrically extendible and ρABB′ a symmetric extension. What we are essentially asking here is whether there exists a copy of Bob’s quantum system that is indistinguishable from Alice’s point of view.
Determining whether a quantum state is symmetrically extendible is not as easy as it might initially seem. In fact, we can currently only do it analytically for two very special types of states, states on two qubits and states on two qudits with several symmetries. Fortunately, using semi-definite programming, we can determine the symmetric extendibility of any quantum state.
- Extendibility of bosonic Gaussian states [arXiv] [Physical Review Letters] [slides]
Ludovico Lami, SK, Gerardo Adesso, Mark M. Wilde
Relevant papers: arXiv:1310.3530v2, arXiv:0906.5255v1, arXiv:0812.3667v1
Extreme limits of quantum key distribution and bound secrecy
Symmetrically extendible states (see above) turn out to be extremely important for quantum key distribution. In QKD, we are interested in how much information any eavesdropper (call her Eve) might have about the secret key Alice and Bob are trying to create between them. Since they use quantum systems to do this by the very nature of QKD, the states describing these quantum systems can be used to determine how much secret key, if any, they can create.
It turns out that if the state ρAB describing Alice and Bob’s quantum systems is symmetrically extendible, then since the system B′ is a copy of Bob’s system and is not in Alice or Bob’s possession, we cannot rule out the possibility that it belongs to Eve. This means that Bob and Eve could be indistinguishable from Alice’s point of view, which means that Eve will know just as much as Bob does about the information Alice is communication during the secret key creation process. This means that no secret key can be created if we just allow for communication from Alice to Bob.
They might still be able to create a secret key if we allow for two-way communication, meaning that we allow Bob to communicate some information as well, which might break the symmetry between himself and Eve. This has been the subject of my Master’s thesis research, in which we considered a particular kind of QKD protocol in the case when Alice and Bob are symmetrically extendible and no protocol has been found to date. We have numerical evidence to suggest that two-way protocols don’t exist. If this turns out to be true, then not only would we have a resolution to this long-standing QKD problem, but we would also have a proof for the existence of bound secrecy, which is a kind of correlation that contains secrecy but that secrecy cannot be extracted into a secret key.
- Numerical evidence for bound secrecy from two-way post-processing in quantum key distribution [arXiv] [Physical Review A]
SK, Norbert Lütkenhaus
Poster presentation at QCMC 2016, QCRYPT 2017. - Symmetric Extendability of Quantum States and the Extreme Limits of Quantum Key Distribution [Master’s thesis]
Relevant work: Geir Ove Myhr’s PhD Thesis, arXiv:0812.3607v2